When a Competitor Can't Compete
A year-long story of cyber attacks, investigation, and confirmation-
and why transparency matters in our industry.
For the past year, we've been dealing with something we had never before faced in our 20+ years of business: coordinated cyber attacks from a competitor. Until recently, we couldn't be sure or prove it. But on October 20, 2025, that changed.
We're sharing this story because many of you in our industry work with or refer business to the organization involved. You deserve to know how they operate when faced with competition.
How It Started
In 2024, we launched a limited beta of ListDefender. We knew we'd face some competition-that's healthy and normal. What we didn't expect was what came next.
Shortly after our beta launch, we learned that Mihir Dhandha (Idea Squad, Inc.), who runs competing services, SpamKill Inc. and SpamClean Inc., went to one of our mutual marketing automation platform providers and attempted to get them to shut us down. Fortunately, this platform partner refused to shut us down.
When that didn't work, things took a different turn.
The Attacks Begin
In late 2024, we started experiencing something we'd never seen in our 20+ years of running online services: coordinated, sustained cyber attacks against our web forms and applications.
Like anyone else doing business on the internet, we'd seen our fair share of junk form submissions and bot attacks, but these weren't typical bot attacks. Someone was flooding our forms with hundreds of submissions using real people's email addresses-email addresses belonging to people who had nothing to do with the submissions. The attacks would last hours to days, then stop. Then start again weeks later.
At first, we were caught off guard. But we quickly got to work.
Building Our Defense (and Gathering Evidence)
Over the next several months, we introduced dozens of improvements to ListDefender and FormDefender. We implemented sophisticated device fingerprinting, device-aware rate limiting, and advanced pattern recognition. Our goal was twofold: protect our customers and gather data about who was behind this.
Over the course of the year, these attacks happened several more times. And they didn't stay confined to ListDefender. They started going after our other properties: PlusThis, TagGenie, Slottable, and SixthDivision.
As our form defenses got stronger, the tactics shifted. When form and account registration attacks stopped working, they started abusing our Calendly scheduling links and Intercom help portals. They even subscribed our help email addresses to hundreds of podcasts and newsletters via Substack, Beehiiv and other similar services.
Someone was spending a LOT of time and energy to cause us problems.
The Bounty
By this point, we'd successfully mitigated nearly all the risk to our systems. We could have just left it alone. But as the attacks escalated and spread to our other properties, we decided to take a different approach.
Based on the data we collected and the pattern these attacks followed, we suspected that someone was hiring others to perform these attacks. So on October 17, 2025, we created a bounty program offering a cash reward for information leading to who was behind the attacks.
We targeted five specific devices we knew were associated with the attacks. When any of those devices tried to interact with our services, we redirected them to a web page that explained the bounty.
One Day Later
On October 18, 2025-a day after launching the bounty-we received an email from "Masu Pi" (an alias, which we will use here rather than his real name). The subject line read: Verify the service sending information to the website.
"Hello Listdefender.com team. I am sending a message to confirm that this is a service that your team or an individual in your team has hired me to do for the purpose of testing the service you are developing, sending requests to the forms on the Listdefender.com website."
"If this is you, please confirm that you requested it and I will continue. If it is not you or an individual in your team, please let me know."
"Also, if this is not a request from your company, I can provide information from the exploit to make your product more effective. I respect the products in development."
- Masu Pi
Think about that for a moment. This developer had been told by his client that he was legitimately testing our service. He reached out to verify before continuing his work.
We responded immediately, explaining that no, we had not hired him, and that we'd like to pursue legal action against whoever did. We offered the bounty in exchange for evidence.
The Confession
What followed was a series of exchanges where the developer, Masu, initially protected his client, then reconsidered after understanding he'd been lied to and manipulated. He revealed that he believed his customer was affiliated with our company and the customer had waited three months for him to build "spam software" specifically for our service.
"His headquarters address is in a different country than your headquarters. Just for fun, because I am busy with other things, so He waited for me for 3 months just to make spam software for your website, if not your team then he must be your big enemy, hahaha."
- Masu Pi
After the back and forth, Masu provided the name of the company that hired him:
"I will start providing you:
Company name that paid me: Idea Squad Inc.
Contact name: Unknown name, On the contact email and github, I see the name Mihir."
- Masu Pi
And that's not all. Masu handed over payment receipts and over a year and a half of internal correspondence originating from Idea Squad Inc.
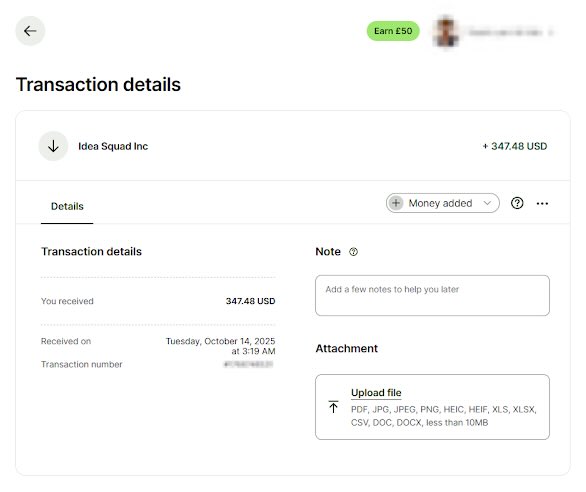
One of many payments from Idea Squad Inc to Masu Pi
One of many notable excerpts from the chat logs provided by Masu Pi
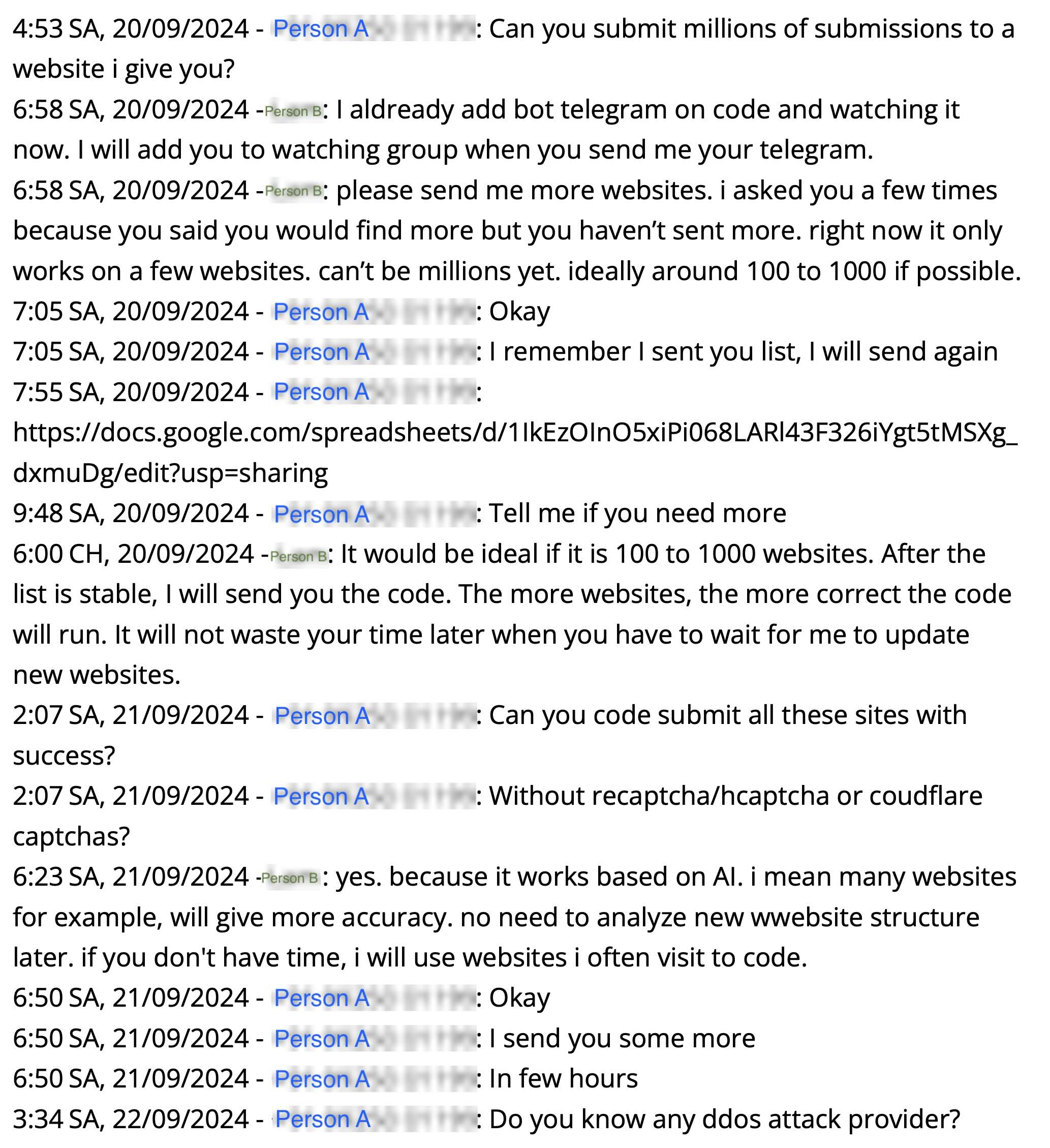
- We’ve redacted names and contact information. Person B is Masu Pi. Person A is an agent of Idea Squad Inc, based on the chat context and payments which are referenced in the chat.
- Link from chat log (link is working, as of December 2, 2025): https://docs.google.com/spreadsheets/d/1IkEzOInO5xiPi068LARl43F326iYgt5tMSXg_dxmuDg/edit?gid=0#gid=0
- We made a copy of the file as a backup, should the original be deleted. The copy can be found here.
- Update December 5, 2025: It appears the spreadsheet linked to above, which was pulled from the chat logs, has been deleted. You can use our backup copy to view the original contents.
Key points to highlight:
- “Can you submit millions of submissions to a website i give you?” (submitting millions of fake contacts with real emails quickly destroys sender reputation and deliverability of any email marketer)
- Link to spreadsheet with 86 websites we suspect were attack targets - many are well-known partners and influencers with a request “Can you code submit all these sites with success?”
- “Without recaptcha/hcaptcha or coudflare captchas” (intentionally bypass form protection)
- “Do you know any ddos attack provider?” (continued intent to expand types of attacks)
It appears from these chat logs that the attacks extended well beyond our own websites — they potentially attacked dozens of others with expanding sophistication and depth of attacks.
The Unexpected Silver Lining
Here's the irony: what was meant to harm us made our product significantly better.
When you're building a product designed to protect against bots and malicious form submissions, there's no better stress test than a year of coordinated attacks from someone who hired developers to build custom software specifically to breach your defenses.
Today, ListDefender and FormDefender can block both automated and human-driven attacks with remarkable effectiveness. We've implemented:
- Behavior detection
- Advanced pattern recognition that identifies malicious behavior before it causes damage
- Real-time adaptation to new attack vectors
- Sophisticated device fingerprinting that can track attackers even as they change IP addresses (optional)
- Device-aware rate limiting that adapts in real-time to attack patterns (optional)
Our customers are now protected by defenses that were battle-tested by a determined adversary with custom-built tools. That's not something every product can claim.
Why We're Telling You This
We believe transparency matters in business. Many of you work with, partner with, or refer clients to people in this industry. You deserve to know how they respond when they face competition.
In this case, when faced with a new competitor, Mihir and his companies (Idea Squad Inc. / SpamKill Inc.):
- First attempted to use influence with our mutual platform partner to have us shut down
- When that failed, hired a developer to build custom attack software
- Misrepresented the purpose of that software to the developer who built it
- Conducted sustained attacks over the course of a year across multiple platforms
This goes beyond competition — we believe it was a coordinated attempt to disrupt our business operations and undermine email deliverability.
What Now?
We're sharing this information so you can make informed decisions about who you work with and recommend.
On November 13, 2025, our attorneys issued a cease & desist to Mihir and IdeaSquad/SpamKill/SpamClean with a required response date of November 29, 2025.
We have yet to hear a response.
We're continuing to focus on what we do best: building products that protect our customers' email deliverability and give them peace of mind. Though the attacks have been very disruptive, they’ve made our products better than we ever imagined they'd need to be.
Updates
January 15, 2026
Since publishing this page, we've received overwhelming support from customers, partners, and industry leaders who reviewed the evidence and drew their own conclusions. Several SpamKill partners and affiliates have requested that their names, logos, and testimonials be removed...
January 15, 2026
Since publishing this page, we've received overwhelming support from customers, partners, and industry leaders who reviewed the evidence and drew their own conclusions.
Several SpamKill partners and affiliates have requested that their names, logos, and testimonials be removed from SpamKill's website. Others have publicly and privately distanced themselves after reviewing the documentation we shared. This response matters because it reflects how the broader ecosystem evaluated the facts — not how we framed them.
We also want to address the public response from Idea Squad / SpamKill leadership.
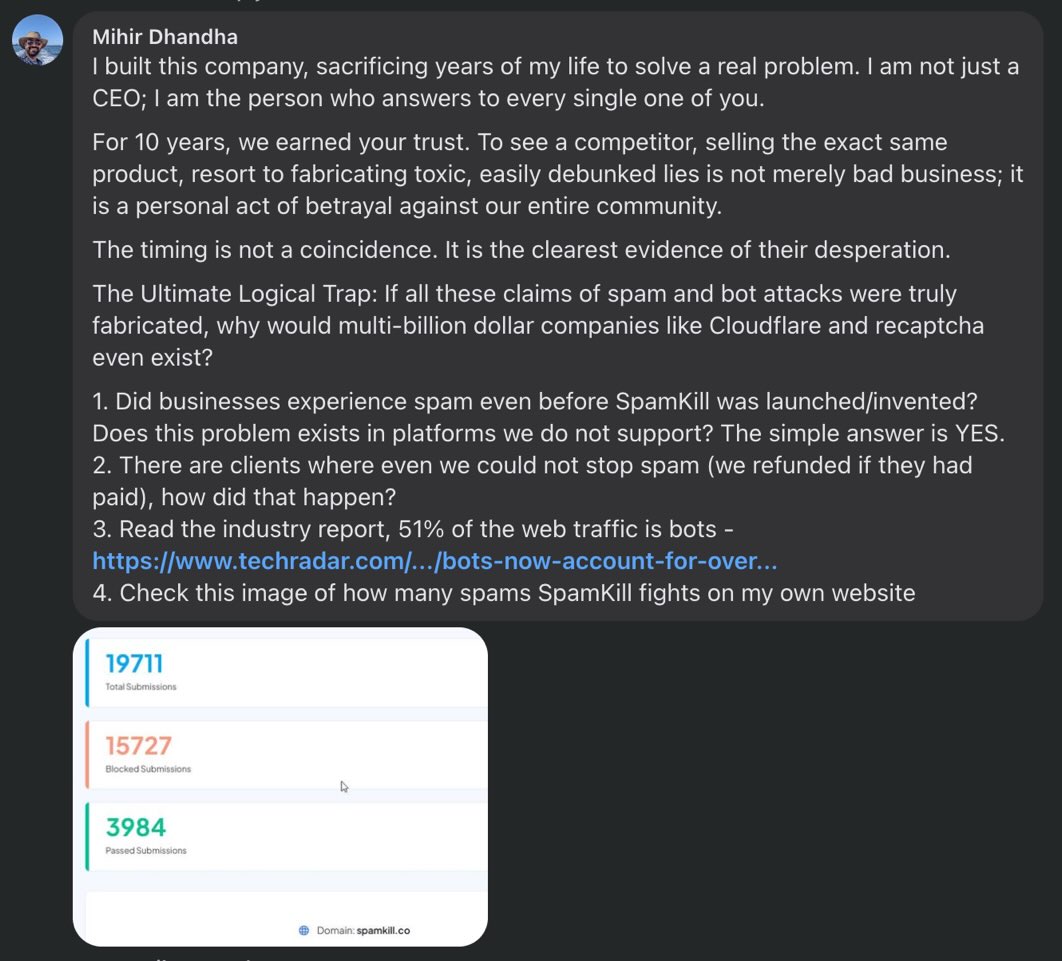
Notably, his statements did not dispute any of the core factual claims presented here:
- He did not deny the existence of payment records.
- He did not deny hiring third-party developers.
- He did not deny that those developers were tasked with form submissions, CAPTCHA bypassing, or bot activity.
- He did not claim the receipts, chat logs, or artifacts were fake.
Instead, his response focused on the general existence of spam on the internet — a topic that was never in dispute. Our claims have always been narrow and specific: that funded, targeted form-spam attacks were directed at our businesses, partners, and competitors.
Finally, since this page went live, one of our founders' personal business email has been used in hundreds of automated newsletter and account signups designed to flood his inbox. We are documenting this activity and preserving records. While we are not attributing this to any specific party at this time, it is consistent with the type of retaliation often seen after whistleblowing or public disclosure.
We have still not yet received a response from Mihir/Idea Squad Inc. regarding the cease and desist we sent on November 13, 2025. We will continue to update this page as new developments occur.
December 8, 2025
The Google Sheet containing website URLs and linked in the chat logs, which is ostensibly controlled by Idea Squad Inc., was deleted or unshared last week. We have still not yet received a response from Mihir/Idea Squad Inc. regarding the cease and desist...
December 8, 2025
The Google Sheet containing website URLs and linked in the chat logs, which is ostensibly controlled by Idea Squad Inc., was deleted or unshared last week, on or around December 5th. We had created a copy to guard against this possibility, and it can be found here.
We have still not yet received a response from Mihir/Idea Squad Inc. regarding the cease and desist we sent on November 13, 2025.
Interestingly, we observed a correlation between our actions and the malicious activity. Following our November 13 cease and desist, the attacks dropped off significantly. However, shortly after publishing this story, the attacks picked up for several hours before dropping off again.
The timeline suggests a peculiar, but notable, coincidence between our public and legal actions and the activity of those targeting us.